Portfolio
Is Contract Testing the Missing Link in Your Microservices Strategy?
Published on Ambassador
How Phishing is Evolving in the World of AI
Published on Computer Weekly
Running APIs in Kubernetes Clusters: Architecture, Scaling & Best Practices
Published on Ambassador
Securing IoT Microgrids: Navigating the New Frontier of Cyberthreats
Published on RSA Conference
How Cybercriminals are Selling Stolen Credentials Like a Marketplace Commodity
Published on Prey
Bridging the IT/OT Divide with an ICS Zero Trust Model
Published on Manufacturing.net
Protobuf vs JSON: Performance, Efficiency, and API Optimization
Published on Ambassador
IDE vs. Traditional Coding: Which Approach Boosts Productivity?
Published on Ambassador
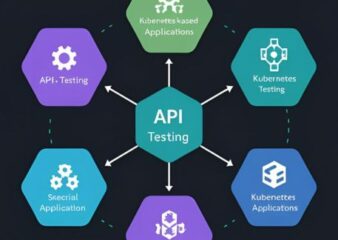
API Testing in Kubernetes: Ensure Stability Across Environments
Published on Ambassador
Quantum Networking and Its Implications for Multicloud Security
Published on SiliconAngle
Zero Trust for IoT Devices: Securing the Most Vulnerable Link
Published on RSA Conference
The Role of Digital Transformation Audits
Published on ISACA
Incident Response Documentation: Building for Resilience, Not Just Recovery
Published on RSA Conference
Quantum Computing in Cyber Security: A Double-Edged Sword
Published on Computer Weekly
Top 5 Hacks to Automate Boilerplate Code and Boost Productivity
Published on Ambassador
Advanced Ransomware Evasion Techniques in 2025
Published on Tripwire
Self-Healing Networks: The Next Evolution in Network Management
Published on Computer Weekly
Accelerating API Prototype Development with Mocking Techniques
Published on Ambassador
Key Practices for Building Secure APIs
Published on Ambassador
Countering AI-Augmented Social Engineering Part 2
Published on RSA Conference
Countering AI-Augmented Social Engineering Part 2
Published on RSA Conference
Enhanced Password Security Crucial in the Wake of Data Breaches
Published on Security Info Watch
Enhancing Data Management with Integrated Platforms
Published on Manufacturing.net
The Role of AI in Threat Detection
Published on Beyond Trust
Automated Patch Management: A Proactive Way To Stay Ahead of Threats
Published on Computer Weekly
Thwarting Phishing Attacks with Predictive Analytics and Machine Learning in 2024
Published on Petri
From Basics to Real-Time Performance: a Complete Guide to API Requests
Published on Ambassador
Green Algorithms – The Environmental Cost of Code
Published on IEEE Computer Society
Beyond VPNs: The Future of Secure Remote Connectivity
Published on Computer Weekly
In-Depth Guide to Open API Specification
Published on Ambassador
Mastering CI/CD Pipeline: The Key to Streamlined Software Delivery
Published on Ambassador
Advanced API Development Tools: Enhancing Security, Scalability, and Efficiency
Published on Ambassador
The Rise of Quantum-Resistant Cryptography
Published on IEEE Computer Society
Ethical Hacking Challenges in AI Data Training
Published on ISACA
The Keys to Successful Zero Trust Implementation
Published on Manufacturing.net
Forensic Cyberpsychology: Profiling the Next-Generation Cybercriminal
Published on Tripwire
The Role of Employee Training in Fortifying Manufacturing Cyber Defenses
Published on Manufacturing.net
The Critical Role of Cybersecurity in Protecting IoT-Enabled Medical Devices
Published on RSA Conference
The Critical Role of Cybersecurity in Protecting IoT-Enabled Medical Devices
Published on RSA Conference
Optimizing the API Lifecycle: A Complete Guide
Published on Ambassador
Securing Supply Chain Data with Advanced Encryption
Published on Manufacturing.net
Top 10 KPIs Every CISO Must Know
Published on RSA Conference
Cybersecurity Best Practices for Legacy Manufacturing Systems
Published on Manufacturing.net
Comprehensive Guide to API Development
Published on Ambassador
Zero Trust Architecture: Cybersecurity Panacea or Puzzle?
Published on RSA Conference
Defending Against Supply Chain Spoofing in Critical Manufacturing
Published on Tripwire
Securing the edge: A new battleground in mobile network security
Published on ComputerWeekly.com
Trends, Best Practices, and Cybersecurity Implications
Published on RSAConference
Emerging Trends in Quantum Computing
Published on IEEE Computer Society
Advancements and Pitfalls in Modern Authentication
Published on RSA Conference
IIoT and its Cybersecurity Implications
Published on Manufacturing.net
Your Guide to OSINT in Corporate Security
Published on RSA Conference
Navigating the New Waters of AI-Powered Phishing Attacks
Published on Tripwire
Leveraging Blockchain for Enhanced Cybersecurity in the Financial Sector
Published on IT Governance USA
Biometric Revolution in Iam: The Future of Authentication
Published on Computer Weekly
Protecting IP in the Age of Industrial Espionage
Published on Manufacturing.net
Decoding Zero Trust in Endpoint Security: A Practical Guide for Cisos
Published on ComputerWeekly
AI and Machine Learning: The Double-Edged Sword in Cybersecurity
Published on RSA Conference
The Complete Guide to Fake Windows Updates
Published on Any.Run Blog
Demystifying Cyber Threat Intelligence: Strengthening Your Security Posture in 2023
Published on IT Governance
Cyberthreats in the Modern Supply Chain
Published on Manufacturing.net
Securing IoT Ecosystems: Navigating Challenges in Industrial IoT Networks
Published on RSAConference
Fortifying IoT Devices: Unraveling the Art of Securing Embedded Systems
Published on Tripwire
Unveiling Hidden Threats Through Advanced Analytics
Published on RSAConference
Ransomware Resilience: Strengthening Your Defenses for 2023’s Threat Landscape
Published on IT Governance
Defending the Factory of the Future
Published on Manufacturing.net
Using JSON Schema for Custom API Responses
Published on Stoplight
Zero Trust Microsegmentation in Hybrid Cloud Environments
Published on RSAConference
Enhancing GDPR Compliance in 2023 and Beyond
Published on IT Governance
Strategies for Making the Most of Your Web Hosting Budget
Published on Hosting Journalist
Focus on These Three Zero Trust Priorities in 2023
Published on RSAConference
Using API Caching to Enhance Web Applications
Published on Stoplight Blog
Using API Caching to Enhance Web Applications
Published on Stoplight
What Does a Cookieless Future Look Like?
Published on IT Governance USA Blog
Threat Modeling in 2023–What Are Its Advantages?
Published on RSAConferece
Enhanced Data Analysis with Synthetic Datasets
Published on Tripwire
Manufacturing Segments that Face the Greatest Cyber Risks
Published on Manufacturing.net
An Introduction to Domain Name Registration and Management
Published on Hosting Journalist
Securing Aviation Systems with Cybersecurity
Published on RSAConference
Can Zero Trust Help Protect Health Care Security?
Published on IT Governance USA
Expert Blog: The Pros and Cons of Shared vs. VPS Hosting
Published on Hosting Journalist
Healthcare API Solutions Improving Patient Outcomes
Published on Stoplight
Why We Need Advanced Malware Detection With AI-powered Tools
Published on ComputerWeekly
Investing in Zero-Trust Cybersecurity Infrastructure
Published on Manufacturing Business Technology
How To Combine Cyber Resilience and Cybersecurity for Maximum Cyber Protection
Published on Tripwire
May 2023 CMMC Rulemaking: It’s Time to Get CMMC Certified
Published on IT Governance
AI Integration: How To Integrate AI With Existing Systems for Maximum Benefits
Published on My TechDecisions
Will AI Be the Start of Super Malware?
Published on ANY.RUN
What to Know For Better API Security Beyond the Design Phase
Published on Stoplight
A Pentester’s Guide to Strengthening Your Cloud Security Defenses
Published on The SSL Store
Synthetic Identity Fraud: What It Is and How to Recognize It
Published on RSAConference
Healthcare Supply Chain Attacks Raise Cyber Security Alarm
Published on Tripwire
Top Open-Source Data Technologies of 2022
Published on RSA Conference
How Payment Service Providers Can Shape Their Anti-Financial Crime Strategy
Published on RSAConference
How to Troubleshoot Microsoft 365 Login Problems
Published on Petri
Why Artificial Intelligence Is the Future of Cybersecurity
Published on Impact Networking
Boosting Your Mobile Retail App Security before the Holiday Season
Published on RSAConference
What is the Principle of Least Privilege?
Published on Illumio
What Is a Red Team? 5 Tips for Safe Red Teaming
Published on Hashed Out
API Security: How to Take a Layered Approach to Protect Your Data
Published on Infosec Resources
Attack Vector vs. Attack Surface: All You Need To Know
Published on PhoenixNAP
Are Protection Payments the Future of Ransomware? How Businesses Can Protect Themselves
Published on Tripwire
Digital Ad Fraud: What is it?
Published on Abusix
ICS Security in Healthcare: Why Software Vulnerabilities Pose a Threat to Patient Safety
Published on Tripwire
Why Your Organization Should Implement a Security Operations Center (SOC)
Published on Abusix
How to Implement a Zero Trust Security Model in a Wide-Open Landscape
Published on Illumio
How To Prevent and Detect log4j Vulnerabilities
Published on NXLog
Is Social Networking a Security Risk for You and Your Business?
Published on Abusix
Is a Private Cloud More Secure Than a Public Cloud?
Published on Abusix
5 Steps That Must be Taken to Improve Defensive Posture Against Insider Threats
Published on Abusix
How To Prevent and Defeat Cybercriminals with Honeypot Traps in Network Security
Published on Abusix
How to Choose a Strong Password
Published on Privacy Australia
How to Get Unbanned on Twitch
Published on Privacy Australia